Fortinet Container Security
Container technology enables developers with new ways to design and develop applications in a more modular and resilient manner.
This is accomplished by separating different logical functions of applications into separate containers for reasons of code life-cycle management and scalability. Further, by breaking applications out into different logical functions—namely, microservices—container technology enables enhanced portability of microservices and applications across different public and private cloud environments.
Due to the radical shift in application architectures, many organizations find that current security solutions are inadequate to address the risks associated with container technologies. This gap forces them to purchase point security products to protect their container environments and force-fit them into the new application life cycle associated with container technology.
The Fortinet container security strategy offers multiple solutions that address the entire life cycle of container-based applications, providing comprehensive protection against threats associated with the different threat vectors to which container-based applications are exposed.
The Key Attributes of Container Security:
- Container-aware security
- Container-enabled security
- Container-integrated security
- Container registry security
The Fortinet container security strategy offers multiple solutions that address the entire life cycle of container-based applications:
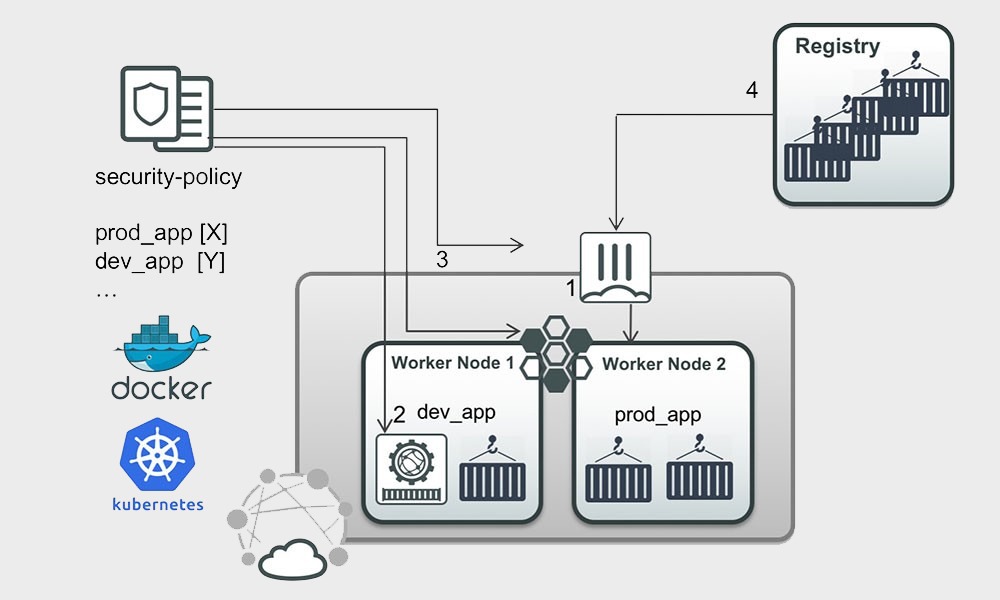
- Container-aware security with the FortiGate Cloud Connector enables awareness of container labels when defining security policies.
- Container-enabled security with FortiWeb as a container image can be bundled within an application chain.
- Container-integrated security allows a Fortinet solution to be dynamically integrated into Kubernetes clusters and inserted in the application chain.
- Container registry security with FortiSandbox scans pulled, pre-configured container images for zero-day threats.
Together they provide comprehensive protection against threats associated with the different threat vectors to which container-based applications are exposed.






